This tip arrived in my email today via the CLA distlist.
Facebook continues to gather your browing history … this link provides some info on how to block it.
Thanks to Toni Samek for the head’s up.
-PC-
This tip arrived in my email today via the CLA distlist.
Facebook continues to gather your browing history … this link provides some info on how to block it.
Thanks to Toni Samek for the head’s up.
-PC-
There has been the beginnings of an interesting discussion this week on the Children's Writer's and Illustrator's chat board. Apparently the already undersized NF sections in bookstores are shrinking rapidly. Word is, no one is interested in these subjects, least of all those boring ol' historical topics.
I'm convinced we here at I.N.K. have the charm, wit, and good looks to do what has never before been successfully attempted. That's right-- we can recommend the near perfect NF selection for any NF neophyte. Yes, it's the NF blog handsell.
Examples? Yes, of course.
You say you really enjoyed the terrific humor and insights of the recent Newbery honor winner THE WEDNESDAY WARS? Well, let me tell you, if you liked those rats, you'll be blown away by Oh, Rats! The Story of Rats and People by Al Marrin. It's rats through the ages, reproducing and thriving, even in a court of law.
Are you the more sensitive type who usually enjoys a tender tearjerker like Jenny Downham's BEFORE I DIE about a girl's battle with incurable cancer? We NF people do diseases--and lots of them. Why not give ace NF writer James Cross Giblin's When Plague Strikes. The Black Death, Smallpox, AIDS a try? Mr. Giblin does not disappoint in his ability to totally immerse his readers in infection, illness and disease.
Please chime in with your best blog handsell.
 On Thursday, I posted about the Meanest Mom in the World. Yesterday, I posted about how I'm trying to catch up with technology. One of the things I was curious about, was the appeal of IMing. Check out the comments about it.
On Thursday, I posted about the Meanest Mom in the World. Yesterday, I posted about how I'm trying to catch up with technology. One of the things I was curious about, was the appeal of IMing. Check out the comments about it.
Today, this leads me to a totally different question. I've wondered about this one for awhile and am now going to put it out there to see what you all think. Put your teenager hat on, your parent hat on, your arguing for the sake of arguing hat on, your how could you hat on, or whatever you want to. I'd really be curious to hear it all, for the sake of research.
Here's the scene:
Mom finds out from reading her sixth grader's IM messages from her cell phone, that her daughter-A, has a boyfriend. A's boyfriend-M, wants A to go over to his house after school during one of the early dismissals. M writes to A, "Nobody else will be home."
Here's the problem:
Mom snooped. Plain and simple. But, her daughter, A, might be going to boyfriend's empty house, doing who know's what.
More on Problem:
When I was growing up, teenagers had diaries, journals, letters or notes that any Mom around the world could be able able to read if they dared to violate their child's trust to find out what was going on.
Today's teen doesn't need a simple lock on their diary anymore. Nowadays, teens have at their fingertips an assortment of technologically savvy tricks to get around Mom and Dad. There are passwords. There are spycams. Secret identities on the web. And more that I haven't mentioned and probably don't know about.
I can only imagine, teens will find more interesting ways to hide secrets from their parents as the technology advances.
Here are the questions:
1. Is this bit of invasion of privacy considered bad form?
2. Why?
3. If not, when is the invasion of privacy considered going over the line?
4. How should Mom deal with A, so the trust isn't completely broken off?
5. What will A do to hide things from Mom in the future?
Put your teenager hat on, your parent hat on, your arguing for the sake of arguing hat on, your how could you hat on, or whatever you want to. I'd really be curious to hear it all, for the sake of research. (Edited to add: I have a scene in a manuscript I've had difficulty trying to figure out the outcome. So I'd so appreciate your help on this one.) No judgements will be made here. All I ask is to keep this conversation respectful. Thank you!
James B. Rule, author of Privacy in Peril: How We are Sacrificing a Fundamental Right in Exchange for Security and Convenience is Distinguished Affiliated Scholar at the Center for the Study of Law and Society at the University of California, Berkeley and a former fellow of the Center for Advanced Study in the Behavioral Sciences at Stanford University. He is also a winner of the C. Wright Mills Award. Privacy in Peril looks at the legal ways in which our private data is used by the government and private industry. In the article below Rule reflects on an article that claims that the average American is caught on film 200 times a day.
China is gearing up for the 2008 Olympics in Beijing—determined to ensure that no demonstrations, terrorist events or unruly crowds mar the bright face it intends to show the world. To that end, the Party leadership is mobilizing sophisticated technologies to keep track of potentially disruptive personalities. Relying on IBM and other western companies, the authorities are planning to monitor the movements of crowds by computer and to respond instantly to any hint of trouble. (more…)
If anyone else is still knee-deep in the new Privacy Report like I am, then this headline might have caught your eye:
Ask.com Puts a Bet on Privacy(NYT)
James B. Rule, author of Privacy in Peril: How We are Sacrificing a Fundamental Right in Exchange for Security and Convenience is Distinguished Affiliated Scholar at the Center for the Study of Law and Society at the University of California, Berkeley and a former fellow of the Center for Advanced Study in the Behavioral Sciences at Stanford University. He is also a winner of the C. Wright Mills Award. Privacy in Peril looks at the legal ways in which our private data is used by the government and private industry. In the original article below Rule looks at a seemingly innocuous effort to track schoolchildren and the issues it raises.
If you increasingly feel that information about your life is taking on a life of its own—collected, monitored, transmitted and used by interests outside your control—you’re probably not paranoid.
A recent story in Information Week tells of a school in Edenthorpe, England, that is experimenting with electronic tracking of its pupils. The idea is to fit their clothing with RFID tags—tiny radio transmitters—that can enable school authorities to monitor people’s whereabouts throughout the school day. RFID technology is already widely in use by retailers to track merchandise within shops and, some suspect, after purchase by customers. (more…)
So, I don’t make you all sit through my deli.cio.us links auto-posting, but sometimes I have a few unrelated things to share that don’t really have their own full posts to go along with them. So here are a few things that are only sort of library related that I think you might be interested in.
Would a university export its user’s server logs to third parties in any other circumstance? Not without a subpoena. Is it time to call on universities, libraries and other public computing spaces to remove the Google Toolbar? I think so.
originally posted by thegloaming
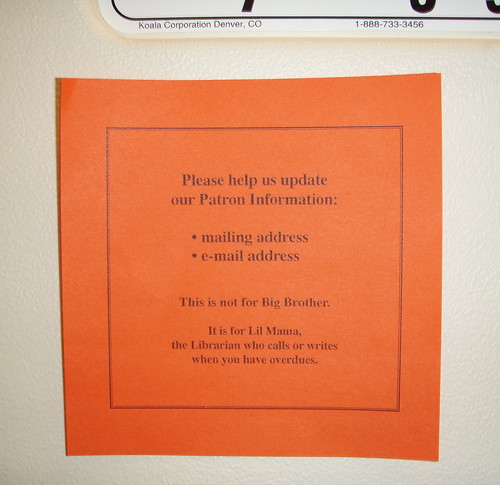
This is my new favorite library sign. I always think you can send a better message using humor than heavy-handedness, although in this case, the librarians are also making a great statement about privacy.
I’ve been mulling over a lot lately the trust librarians have built up with users just through our actions (they speak louder than words, right?). I think there’s a lot we can do here, teaching people (and especially students) how to manage their online identity. “How to be a good digital citizen” should also include how to represent yourself online, in addition to how to participate and media literacy in general.
I’ve also been thinking about “persistence” a lot lately, and I’ll be writing more about that because I think it’s one of our biggest assets in the digital world (from many different angles, too).
In the meantime, I’m happy to see Bloglines has incorporated OpenID, something I wish libraries - and particularly library vendors - would pay more attention to. To learn more about what Bloglines is doing in this area, go to http://www.bloglines.com/about/news and scroll down to the current second item (or just try going here). (Hopefully the folks at BL are in the process of turning this page into a blog so that we can point to specific news in the future, rather than one long page. Wink, wink, nudge, nudge, say no more.) Bonus points to them for adding openID authentication in the first place.
I’d like to think libraries could be influential in educating Americans about the benefits of OpenID and help folks tame some of this chaos. The more sites that use an open standard like this (cough, libraries, cough), the better it is for all of us. And let’s face it, in a situation like this, who are you going to trust - your local library or Big Brother?
big brother, openID, privacy, trust
A quick shout out to Wandering Eyre for the Chronicle mention on gaming and libraries. Whoo-Hoo!
Speaking of serious game-playing, now that OCLC is seriously researching privacy, it seems like I can't turn around without seeing an article on privacy or hearing a radio report on a new threat. Danny Sullivan was on NPR's Marketplace tonight, talking about our relative lack of privacy in the Web world. (The Privacy International report sparked a lot of the talk, I'm sure. Matt's response.)
And thinking about privacy in the Web world leads me to thinking about privacy in libraries. One of the tenets we've been talking about with the advocacy research we're doing, is how U.S. libraries are seen (at least in some consumers' eyes) as a democratic institution, a part of the fabric of life as ingrained as voting and representative government. (Motherhood and apple pie? Death and taxes?) I started to wonder about how private our political lives are--and/or how much they should be. Certainly my vote is private (at least until I slap on a candidate sticker) and perhaps my IRS return is semi-private. What else is? What is not? Why and why not? And how did library records get mixed up in the middle of it?
These are questions that I have no idea if they'll be addressed in the privacy report or not. But I can tell you that once your consciousness is raised about it, privacy concerns are everywhere. My shredder is busy.
In cruising through some leftie-librarian sites, I came across this quick and dirty guide through the fabulous Jenna Freedman’s delicious links, handily available through her blog-under-construction lower east side librarian.
The guide was produced by the Electronic Frontier Foundation.
Check out Six Tips to Protect your Online Search Privacy and feel safer whilst you surf.
As we have done for many years, OCLC will be hosting a Symposium at ALA Annual in DC. It will be June 22, 1:30 – 4:30 pm, at the Grand Hyatt Washington, Independence Ballroom A and registration is here. The topic of this one is related to our forthcoming report Sharing, Privacy and Trust in the Age of the Networked Community.
Title: Is the Library Open?
Hear from three experts on the issues of information privacy law, copyright, digital communication, intellectual property and patron privacy rights in relation to library policies.
The speakers are:
· Marc Rotenberg, Executive Director of the Electronic Privacy Information Center (EPIC) and professor of privacy law at Georgetown University Law Center. "EPIC is a public interest research center in Washington, D.C. It was established in 1994 to focus public attention on emerging civil liberties issues and to protect privacy, the First Amendment, and constitutional values. EPIC publishes an award-winning e-mail and online newsletter on civil liberties in the information age – the EPIC Alert."
· Siva Vaidhyanathan, a cultural historian, media scholar and an associate professor of culture and communication at New York University. He blogs at Sivacracy.net. A journalist before he became a professor, he has written several books (including The Anarchist in the Library: How the Clash Between Freedom and Control is Hacking the Real World and Crashing the System) as well as for many periodicals. And he's been on The Daily Show, but you can't see that clip on YouTube anymore because of the Viacom copyright claim.
· Mary Minow, a library law consultant with LibraryLaw.com, coauthor of The Library’s Legal Answer Book and a public librarian for 10 years. She is the coauthor with Tomas Lipinski of The Library's Legal Answer Book (ALA Editions: 2003). She blogs at LibraryLaw.Blog and says this about herself, "I studied library law, that is the combined study of First Amendment, Copyright, Local Government Law, Disability Law, Negotiations etc. Now what I care about is sharing the most practical parts of the law that I learned, the good, the bad and the ugly, with my former colleagues, the librarians of the world."
These are the surveillance cameras in George Orwell’s London neighbourhood.
via Digg and thisislondon
funny, and ironically disturbing.
Ah, but what did A text back to M? Yes or no? That's where you'll really learn whether you need to step in. Plus, it's really hard to judge from a text message what a teenager is actually going to do. She may say one thing, just to look cool with the idea, and then not follow through with meeting him because she's uncomfortable.
Honestly, I would just ask her what she's doing on the early dismissal day. If she lies, then you have a problem. But maybe she'll tell you that M invited her over. Then you can ask: who will be home?
If she doesn't tell you, then you can bring up the general subject of where she's allowed to be when, and offer to be her backup if she has any concerns. Truly, my kids often used Mean Mom as their excuse for not doing things.
I'm probably in the minority here, but I think it's okay for Mom to intervene. I like what Sara suggests.
I so feel your fear and discomfort, here, hip mama. Aiiiii, Yiiiii, Yiiii.
If it were me: I'd get in the car with my girl, and drive somewhere (to make the conversation easier on both of us, driving makes eye contact impossible). And then I'd be super honest. I snooped. Which I'm not proud of. And I'm sorry about violating your privacy. I'd tell her exactly what I read. And say I'm pretty worried and kinda scared. So--tell me about this guy. Have you kissed? How'd that feel? Etc.
Good luck.
Sara and I are on the exact same wavelength:
First of all, her response to the text message is unknown, so don't jump to conclusions, don't make assumptions.
Then, simply asking her what she plans on doing that day is a gentle opener (nothing harsh, no judgments, no assumptions, no accusing her of something that hasn't happened yet, that may not happen at all) and it is a true and honest question.
Sara,
Thanks for that view. My kids are still young, so I haven't experienced any of this yet. I've only heard some interesting stories from friends. Which gave me this idea for a scene in a manuscript.
I haven't decided how A will answer back, and have two different versions to figure out which will be more realistic.
Thank you!
----
Anonymous,
Thank you.
----
Amy,
That's a cool approach. Find a way to make an uncomfortable situation, comfortable. The no eye contact thing, might make things more palatable. Thanks for this suggestion!
----
LW,
This is good. Thank you!
Oh, we're torturing a FICTIONAL mom! I should've been much harder on her, then. :)
Although I do stand by my basic point. The mom could easily assume that her daughter's going to follow through with the meeting when she's not, and then the daughter gets angry about the snooping, and won't trust her mom because she thinks her mom doesn't trust her. Maybe she even uses fake IM's to mislead her. (how evil!)
But be as mean as you have to! Ratchet up that conflict! :)
Oohh! This sounds like a very pivotal scene. Yes, it is total invasion of privacy. Mom should never have looked at the IM to begin with.
If I were A, I'd probably do what Sara suggested, with the fake IM's. I don't have a cell phone, but isn't there a way to put a password on retrieving those messages? She could also have her friends covering for her, so she could sneak out.
You are welcome. You have email!
Sara,
Fake IM's! Awesome idea! Conflict is very key here, though that is exactly why I have to ask for the input. I don't know all the technology, nor all the teenage tricks, so this is very helpful.
Thank you!
----
Anonymous,
I'll have to ask if there is a way to put a password on the IM's.
I really appreciate your ideas!
---
LW,
Thanks!
It's so hard to know what the right thing to do as a parent. I know for me, I want my children to know I trust them. On the other hand, children grow up so much faster these days and are exposed to more dangerous things when they don't have the maturity to handle it.
And now you've brought up some other things I haven't even thought about, it just about freaks me out.
How am I going to be able to know my kids are safe unless I "snoop" on them? I don't think it makes me a bad mother, just one who takes precautionary measures.
The problem is it will up the ante for my children to try to sneak around me even more, so I'm not sure if there is a win-win situation here.
I reviewed a great book called Logged On and Tuned Out. It would be great research for you, as well as great info for parents of tweens and teens.
The author Vicki Courtney maintains that until children have proven that they can use technology responsibly that it's actually just a part of parenting to be sure that they are. She also talks about how we can actually learn a lot about them by reading their (and their friends) myspace or facebook pages and monitoring IMs (there is software that does this). Anyway, she goes into a lot of detail about the hows and whys, and I agree with her. Her kids know that she monitors, and she only steps in when she thinks it's of utmost importance.
I would think that this situation warranted stepping in--especially if it's breaking a pre-established rule. In that case, the mom has grounds.
My daughter is only nine, but I know all of this is coming--too soon!
Anonymous,
I hear you. Parents do have quite the dilemma, don't we?
----
Jennifer,
Thank you so much for recommending the book! I just checked read through your recommendation, and it sound like the perfect research for me. Thank you!
My eldest is nine, too, so it'll be nice to be prepared ahead of time. Though I'm sure we'll be dealing with something else entirely by the time our kids are teens.
Thanks again!
I have to say that when I was much older than a sixth grader my mother snooped and found out things about me and I was mortified. I was so angry, and I didn't trust her afterward, but I eventually needed her, she was my mother.
I don't think that having a conversation with me would have stopped the situation, but snooping did. I had to make changes because otherwise more severe consequences were going to happen for me.
It was a turning point for me.
Well,
I definitely think Mom stepped over a boundary line. Said teen should have the right to talk to friends without fear of snooping. This is like reading daughter's diary. It's a no no UNLESS there is an understanding at the beginning that Mom will be checking in occasionally, which I know some parents do. Like you can see what your teen is viewing on the internet by viewing history.
You have to try and put trust in your kids and give them the benefit of the doubt. I am going to post this on our library teen blog. I would like to hear what teens have to say about this.